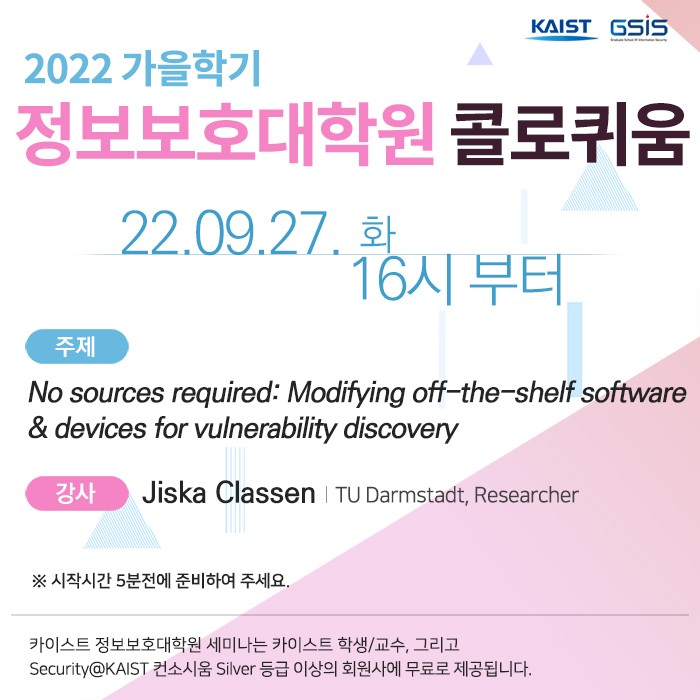
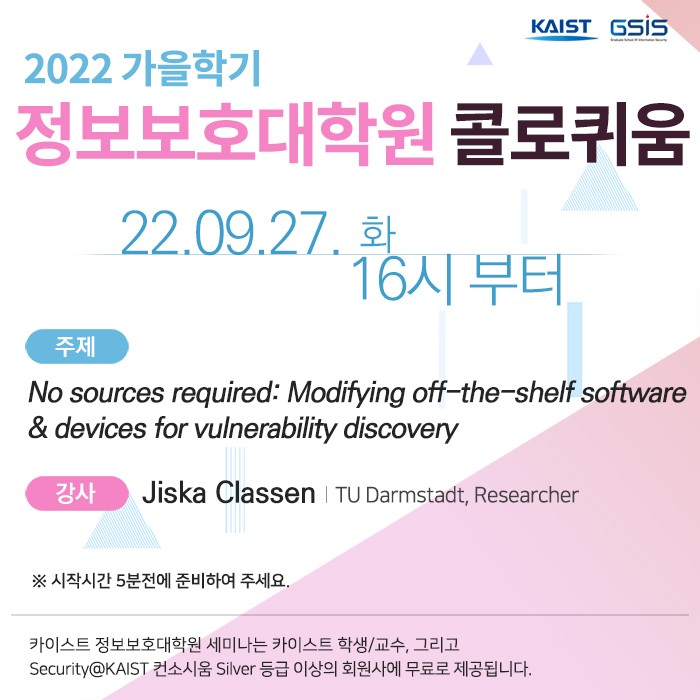
정보보호대학원에서는 9월 27일 오후 4시에 온라인 세미나를 개최하고자 합니다. 많은 참석 부탁드립니다.
o 일 시: 22. 9. 27(화) 16:00~
o 주 제: No sources required — Modifying off-the-shelf software & devices for vulnerability discovery
o 강 사: Jiska Classen (TU Darmstadt, Researcher)
※ 세미나 시작시간 5분전에 준비하여 주세요.
ㅡㅡㅡ
♣ Title: No sources required — Modifying off-the-shelf software & devices for vulnerability discovery
♣ Abstract
Modern devices appear to be black boxes, dominating our everyday life. While they're omnipresent, we only know little about how they work: Which data is collected by your vacuum robot and sent to the cloud? Is the health information on your smartwatch really secure? How do the latest features announced for the iPhone work internally?
Reverse engineering is the process of analyzing how something was engineered to gain insights about its internals. On devices where binary patching is possible - either intended or due to security vulnerabilities - reverse engineering even allows changing the behavior of a black-box device.
In this talk, you will learn about the basic steps of reverse engineering, including real-world examples. Despite the initial effort of learning how to reverse engineer, tinkering with modern devices can be very rewarding. Not only they will no longer be a black box, but often, understanding them will lead to discovering critical security vulnerabilities.
♣ Bio
Dr.-Ing. Jiska Classen is a wireless and mobile security researcher. The intersection of these topics means that she digs into iOS internals, reverse engineers wireless firmware, and analyzes proprietary protocols. Her practical work on public Bluetooth security analysis tooling uncovered remote code execution and cryptographic flaws in billions of mobile devices. She also likes to work on obscure and upcoming wireless technologies, for example, she recently uncovered vulnerabilities in Ultra-wideband distance measurement and reverse engineered Apple's AirTag communication protocol.
She has previously spoken at Black Hat USA, DEF CON, RECon, hardwear.io, Chaos Communication Congress, Chaos Communication Camp, Gulasch Programmier Nacht, MRMCDs, Easterhegg, Troopers, Pass the Salt, NotPinkCon, gave various lectures and trainings about wireless security
and mobile reverse engineering, and published at prestigious academic venues such as USENIX Security and S&P.